Certifications
 CISSP
CISSP
 OSCP
OSCP
 PNPT
PNPT
 OSWP
OSWP
 KLCP
KLCP
 HRM
HRM
Certified ethical hackers delivering penetration testing, vulnerability assessments, physical security, security camera installs, and door access control for businesses that can't afford to find out the hard way.
8 questions. 60 seconds. No email required. Get a personalized security risk assessment based on your actual situation.
Based on IBM Cost of a Data Breach Report data and Verizon DBIR statistics. See what a breach would actually cost your organization — then compare it to what prevention costs.
From external recon to inside your walls — we find the gaps before attackers do. Every engagement is real-world, not checkbox security theater.

A Vordr timeline separating confirmed vendor statements, public reporting, attacker claims, data exposure details, and school-impact caveats.

CVSS 10.0. Remote code execution. No authentication required. If your site runs React Server Components, you need to read this now.
As passwords fade, session tokens become the invisible keys to your kingdom. Vordr breaks down how attackers steal them — and how to stop it.
In April 2025, DaVita Inc. disclosed a ransomware attack that encrypted network segments and disrupted operations. Here's what it means for every healthcare org.
Children are prime targets for identity thieves precisely because they have clean histories. Here's how to freeze your child's credit — even before they have a file.
Data breaches are the new normal. Here's exactly what to do in the next 24 hours and beyond to protect yourself.
It only takes one vulnerability to bring down a business. A pentest finds your gaps before attackers do — here's what's involved and why it matters.
A defective CrowdStrike update took down Microsoft globally — banks, airlines, media. A clear breakdown and lessons for your organization.
Is someone else on your WiFi? Here's how to detect unauthorized devices, kick them off, and lock your network down — step by step.
A credit freeze is one of the most powerful — and free — tools to protect your financial identity. Here's everything you need to know.
Live headlines from top cybersecurity sources — refreshed every visit.
Sources: The Hacker News • Krebs on Security • Bleeping Computer • CISA Advisories
Right now, Yarbo is our featured affiliate partner. We have tested the concept, like the platform direction, and use this section to highlight technology we believe is genuinely worth a closer look.
Every product here has been evaluated through a security lens, not just features. When we link to Amazon, we may earn a small commission. It keeps the lights on and does not change our recommendations.

Phishing-resistant hardware key. One of the strongest upgrades you can make to your accounts, especially for email, admin consoles, and cloud services.
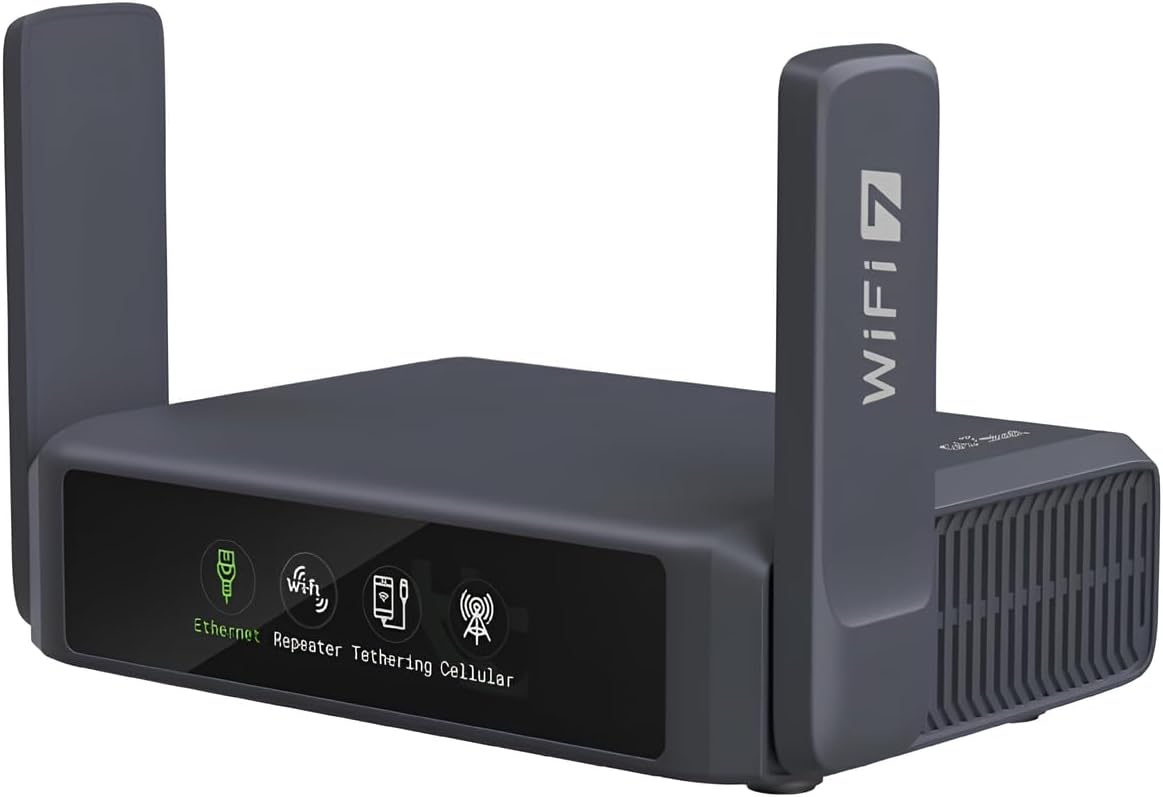
Portable VPN router with real control. Useful for travel, public WiFi, client work, and keeping your devices behind a network you actually manage.

Trace wiring, identify runs, and troubleshoot quickly. Extremely useful for camera installs, access control work, and physical security assessments.

Good fit for homes and small offices that want cameras without turning every feature into a monthly subscription. Practical, visible deterrence.

A stronger option for larger properties, shops, and serious monitoring. More appropriate when you want local recording and a dedicated camera system.
Not cybersecurity gear, but performance matters. A useful read for dialing in energy, recovery, experimentation, and output.
No full pentest. No sales call. Just a real look at what's exposed — delivered to your inbox within 48 hours.
Clicking Start My Snapshot will open your email client with everything pre-filled — just hit send.